Zoom is finally getting this huge upgrade — what you need to know [updated]
Zoom is finally getting this huge upgrade — what y'all need to know [updated]

UPDATED throughout with comments and explanation from Zoom.
Zoom is finally letting coming together participants apply stop-to-end encryption in a trial run, after a couple of earlier announcements that implied such encryption would be bachelor much earlier.
"Starting next calendar week, Zoom's end-to-finish encryption (E2EE) offering will exist available as a technical preview, which means nosotros're proactively soliciting feedback from users for the first thirty days," Zoom Head of Security Engineering Max Krohn said in a blog post yesterday (Oct. fourteen).
- Best complimentary Zoom backgrounds
- Zoom privacy and security issues: Everything that's gone wrong
- Plus: Best Prime number Day deals you tin however become now
"Zoom users — free and paid — around the earth can host upwardly to 200 participants in an E2EE meeting on Zoom, providing increased privacy and security for your Zoom sessions."
This sounds lovely, but as with many things Zoom, the devil is in the details. Beginning of all, information technology's not still clear how to even enable this.
How do yous plow on Zoom end-to-cease encryption?
The Zoom "E2EE" will non be on past default, Krohn explains.
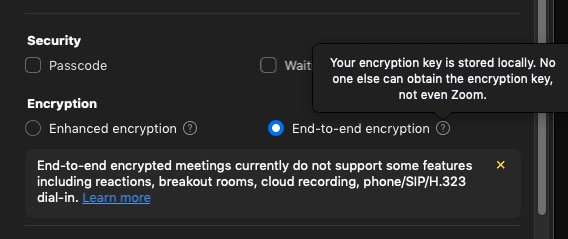
"Customers must enable E2EE meetings at the account level," he states, and the blog post includes a screenshot of what appears to be the settings screen of the Zoom desktop client.
We weren't able to discover any such setting on own fully updated version of the Windows desktop Zoom customer, and trying to adjust our profile settings bounced us to the Zoom website, which once more came up empty.
"It will get available side by side week," a Zoom spokesperson said in response to Tom's Guide'southward questions. "It's incredibly easy to enable in your web dashboard, and when scheduling meetings and participating in meetings."
Even after you enable E2EE, yous will have to "opt-in to E2EE on a per-meeting basis" — and that's only if the meeting host enables it on their terminate.
That may be just as well, considering equally Krohn notes, "Enabling this version of Zoom's E2EE in your meetings disables certain features, including join-before-host, cloud recording, streaming, live transcription, Breakout Rooms, polling, 1:1 private chat, and coming together reactions."
He doesn't mention it, merely we tin't imagine that someone will allowed to join an E2EE meeting if they're calling in from a phone line. And joining from Zoom'southward web-browser interface, rather than from the Zoom desktop or mobile customer software, might also be problematic.
The Zoom spokesperson confirmed both points.
"Zoom end-to-end encryption does not support dialing in by traditional phone line, or browser," the spokesperson told Tom's Guide. "It's difficult to prove when a coming together is truly cease-to-stop encrypted through a browser, which is why we aren't supporting that in stage 1."
"Individual Zoom users will desire to weigh whether they demand these options earlier enabling finish-to-cease encryption in their meetings," the spokesperson added.
How does Zoom'southward end-to-end encryption work?
To get more technical, it'southward foreign that Krohn is using the acronym "E2EE" to refer to end-to-end encryption, when the rest of the computer manufacture uses the more commonplace "E2E."
This makes us wonder is Zoom is again fudging the definition of "end-to-end", every bit it did for years by claiming that information encrypted betwixt the client and the server counted as "end-to-terminate."
Information technology most certainly did not. End-to-finish encryption is when merely the two devices at either end of a advice can read the message. Intermediary parties — network servers, device makers, service providers — should non be able to.
"This is the existent deal," the Zoom spokesperson told Tom's Guide, and referred united states of america to a GitHub page that documents the progress of Zoom's encryption implementation. including a white newspaper from yesterday that Krohn co-authored along with some prominent encryption experts.
"We use 'E2E'to mean 'stop to end,' and use 'E2EE' for 'end-to-end encryption' (three E'south)," the spokesperson added.
Under Zoom's previous "terminate-to-stop" implementation, Zoom's servers could decipher all meetings, which meant Zoom itself had admission to whatsoever was said in those meetings.
That'southward not a problem when it comes to altogether parties and school classes, but government and corporate clients might want to keep their data safe from a company that has extensive operations in China and was founded and is led by a Chinese national.
"Zoom is an American company, publicly traded on the NASDAQ, with a founder and CEO who is an American citizen, with headquarters in San Jose, California," the spokesperson noted.
To resolve that embarrassing state of affairs, Zoom bought an encryption provider called Keybase in May, the results of which we see today.
Who's generating the encryption keys?
Krohn's blog post does not clear things up, because he uses two possibly contradictory explanations of how Zoom'due south "E2EE" will work.
"Zoom's E2EE offering uses public-key cryptography," he says in a FAQ. "In brusk, the [encryption] keys for each Zoom coming together are generated by participants' machines, not past Zoom'south servers."
Correct. That's the way end-to-terminate encryption is meant to work. And then far, so good. (The public-key cryptography does not create the bodily encryption key, but is a fashion to deeply transmit that encryption cardinal to the other participant.)
But earlier in the same postal service, Krohn states that "with Zoom's E2EE, the meeting'south host generates encryption keys and uses public-cardinal cryptography to distribute these keys to the other meeting participants."
That makes less sense. Who exactly is generating the encryption keys? The meeting host, or the other participants' machines?
"It's the host's motorcar," the Zoom spokesperson said in reply to our questions.
Exactly what kind of encryption keys are the meeting participants getting from the host? Are there individual encryption keys for communications between the meeting host and each individual participant, or do all meeting participants share the same encryption key? If hundreds of meeting participants share the aforementioned encryption key, then does it actually count as finish-to-end encryption?
"They all share the same coming together key, only they employ dissimilar public/individual key pairs to communicate that meeting key," the Zoom spokesperson told us after this story was commencement published.
Source: https://www.tomsguide.com/news/zoom-encryption-beta-test
Posted by: houstonsponsiguess.blogspot.com


0 Response to "Zoom is finally getting this huge upgrade — what you need to know [updated]"
Post a Comment